CES 2017: Localized driverless car functions ride on EB software, automotive cybersec fights back in Argus collaboration
January 11, 2017

If you can't make it to the Gold Lot parking lot at CES, sometimes you have to bring the Gold Lot to you. That's exactly what Elektrobit did at CES 20...
If you can’t make it to the Gold Lot parking lot at CES, sometimes you have to bring the Gold Lot to you. That’s exactly what Elektrobit did at CES 2017, with an automated driving demonstration in North Hall that was developed in conjunction with researchers at the University of Munich. In the demo, several toy cars retrofitted with cameras, ultrasonic sensors, MEMS, and compasses navigated around a small track replete with obstacles, along the way obeying traffic laws and avoiding, most notably, each other. The catch here, though, is that none of them were equipped with communications technology – all of the collision avoidance and active safety functions of the driverless cars were performed completely locally.
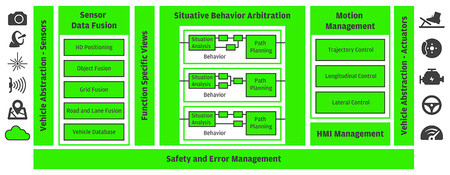
The cars in the demo were outfitted with an ITX motherboard housing an Intel Core i7 processor, and running the hardware-agnostic, AUTOSAR-compatible EB robinos application-layer software platform. As shown in the figure below, EB robinos contains all of the software components necessary for autonomous driving and active safety functions by employing a modular approach that can be tailored to the capabilities of a particular vehicle. Therefore, sensor inputs from various technologies can be abstracted and fed into an architectural block of the EB robinos that handles situation analysis and planning (see Situative Behavior Arbitration), allowing cars to ingest information about their surrounding environment, asses it, and then take a corresponding action based on pre-defined behavior. Speaking of behavior, it was interesting to see the “personality” each car seemed to develop over the course of the demonstration, as at times if there was an obstruction that caused them to wait too long (i.e., one of the other vehicles), they would seemingly become impatient and navigate around it.
“The robinos architecture allows the combination of various technologies, and allows algorithms to run based on the technology present in the vehicle architecture, whether you have them or not.” says Manuela Papadopol, Director of Business Development and Communications at Elektrobit.
As evident in the demo, EB robinos is capable of supporting level 5 on the SAE autonomous driving scale. As a cherry on top, the cars were also supported by the automated valet parking feature of Elektrobit’s EB Assist Automotive Data and Time-triggered Framework (ADTF) software so that when the cars were running low on battery, they simply pulled into a designated area and parked themselves.
Argus partnership yields serious automotive security, all based in software
Automotive security has inundated the headlines since the Jeep Hack about 18 months ago, and given the second half of my meeting with Elektrobit, it appears automakers and their suppliers have taken notice.
While at the Elektrobit booth, I was informed of a partnership between the company and Argus Cyber Security that has yielded an automotive-grade intrusion detection and prevention system (IDPS) integrated with the EB tresos operating system (OS). In the implementation shown (though any electronic control unit (ECU) architecture or implementation can be supported, according to officials from the two companies), the integrated solution had been installed on the gateway ECU of a makeshift vehicle that monitored messages traversing the CAN bus to determine their validity, authenticity, and integrity.
Shown on the tablet is a representation of the vehicle’s systems, and after “hacking” into them I was able to manipulate operations on the actual car platform itself by, for example, increasing the revolutions per minute (RPMs) of the engine, modifying the output of the infotainment system or instrument cluster, or shutting the car off completely. However, through the Argus back end console (shown on the monitor in to the rear of the picture), the yellow bar indicates that messages (and therefore, actions) are being monitored as potentially suspicious. Slightly to the right, you will notice that a red bar is beginning to appear, which indicates that these messages are being blocked, though monitoring continues. In this demonstration, all of this monitoring and intervention is being done remotely through the cloud.
However, another intriguing feature of the solution described by Yoram Berholtz, Business Development Director at Argus is that while blocked messages are no longer being received by ECUs targeted by a particular malware or hacker, this is not discernible by attackers. The adversaries believe that their attack is commencing as planned, which makes the implementation one part cyber countermeasure, one part honeypot/deception network. Since the technology is completely rooted in software, it can quickly be deployed to AUTOSAR-compliant OSs like EB tresos. As far as security is concerned, there, at least, is one benefit of the connected car.